Background
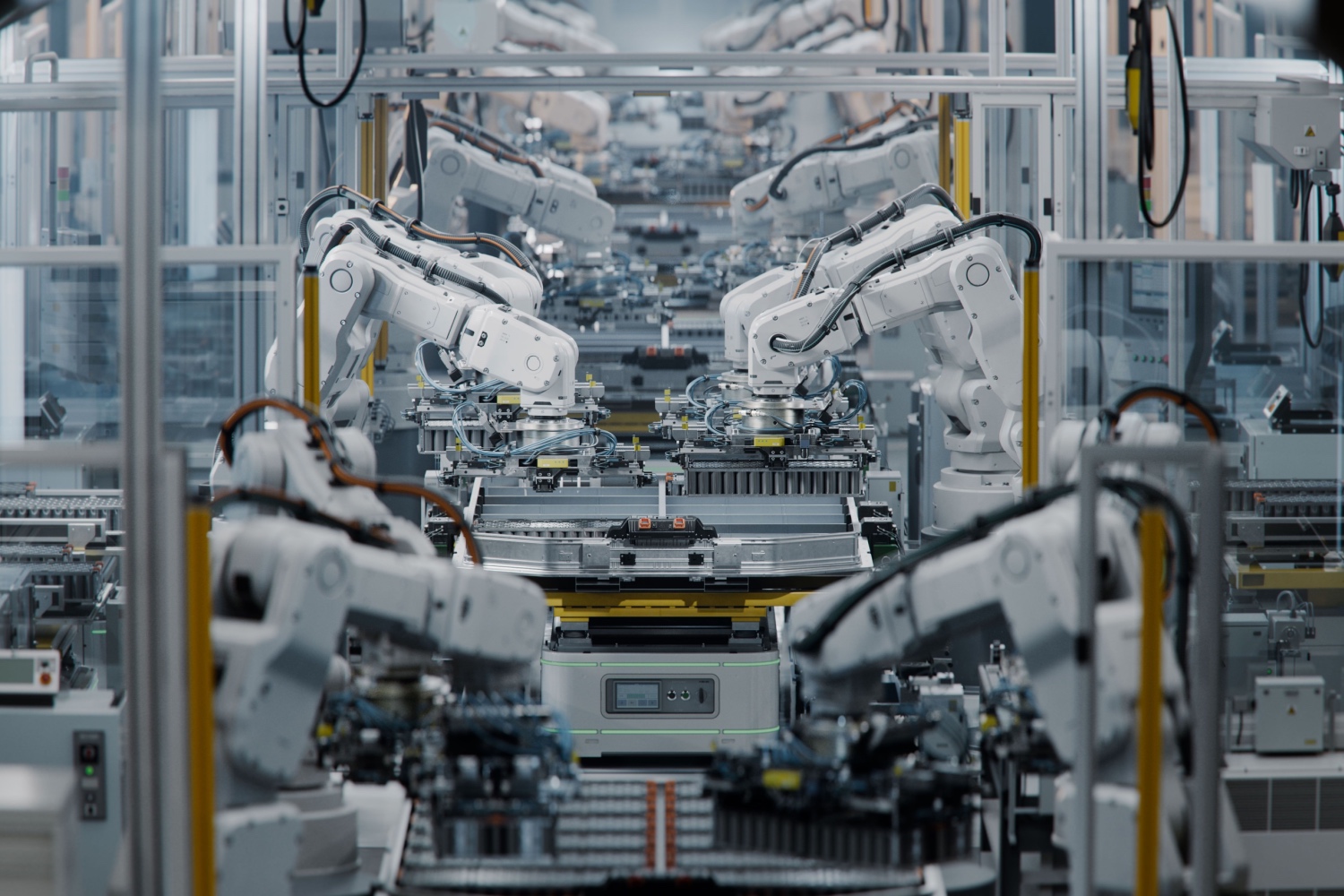
A global high-tech manufacturing company integrated two GenAI apps into its daily operations to improve operational efficiency, reduce manual effort, and accelerate decision-making. The two GenAI apps were designed to:
- Automate critical business operations
- Support document translation
Challenge: Ensuring GenAI Security and Compliance
While GenAI offered significant operational advantages, it also introduced new risks that needed to be addressed. Before scaling these applications, the company aimed to identify and mitigate vulnerabilities with the following objectives:
- Ensure compliance with internal policies in automated processes.
- Validate the accuracy and integrity of the translated documents to prevent misinformation or misinterpretation.
- Assess the resilience of the applications against adversarial attacks that could bypass security measures or compromise data.
- Align with internationally recognized best practices to ensure compliance with global standards, demonstrating the company’s commitment to maintaining security and resilience across its worldwide operations.
Why Vulcan?
After evaluating multiple vulnerability assessment solutions, the company chose Vulcan Attack as their GenAI security partner due to three key differentiators:
- Effective Assessment: With proprietary attack techniques, Vulcan provides more precise and effective assessments than many other solutions, offering deeper insights into vulnerabilities and enhancing risk intelligence.
- Multilingual Testing: Unlike many solutions that focus only on English, Vulcan conducts assessments across multiple languages, including the company’s primary language, ensuring that language- and culture-specific vulnerabilities are effectively identified.
- Compliance Mapping: Vulcan aligns assessment results with international best practices and offers flexibility for local compliance mapping based on client requirements.
Vulcan’s Assessment Process
The company partnered with Vulcan to conduct vulnerability assessments, simulating real-world adversarial attacks to evaluate their GenAI applications’ security and compliance posture. The key steps included:
- Threat Identification: Assessed vulnerabilities in business process automation, document translation and data handling.
- Attack Simulations: Generated targeted test cases to assess resilience, including manipulated data and potential information extraction attempts.
- Mitigation & Optimization Strategies: Provided actionable recommendations to reinforce security, enhance model robustness, and mitigate risks before full-scale deployment.
Outcome
With Vulcan, the company was able to identify vulnerabilities in both applications, helping them:
- Improve GenAI Reliability: Proactive testing helped identify and mitigate vulnerabilities in the GenAI apps, improving overall reliability of GenAI-driven automation.
- Secure Operations: Early insights into potential threats enabled proactive risk management, minimizing operational disruptions and safeguarding proprietary information.
- Enhance Compliance Confidence: Ensured alignment with industry standards and best practices, such as OWASP Top 10 for LLM & GenAI Applications, strengthening AI governance and promoting responsible AI deployment.
Conclusion
The two GenAI apps helped streamline operations but also introduced potential risks. By partnering with Vulcan, the company proactively identified and mitigated vulnerabilities, ensuring the apps remained secure, reliable, and compliant before potential large-scale deployment.
Explore how Vulcan conducts GenAI assessments here, or simply get in touch with us at contact@vulcanlab.ai.
Disclaimer: To maintain client confidentiality, some details in this case study have been modified or eliminated. However, the security challenges, testing methodologies, and key insights accurately represent real-world scenarios and best practices in GenAI security.